Twelve out of 16 Bluetooth smart locks examined could be unlocked by a remote attacker, a researcher said at the DEF CON hacker conference.
Source: 75 Percent of Bluetooth Smart Locks Can Be Hacked
The problems didn’t lie with the Bluetooth Low Energy protocol itself, Rose said, but in the way the locks implemented Bluetooth communications, or with a lock’s companion smartphone app. Four locks, for example, transmitted their user passwords in plaintext to smartphones, making it easy for anyone with a $100 Bluetooth sniffer to pluck the passwords out of thin air.
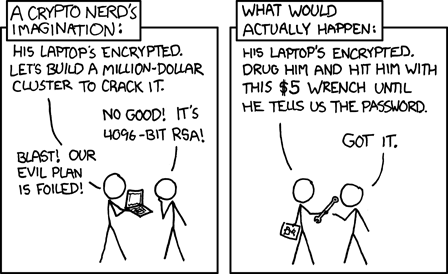
From: http://xkcd.com/538/